hivexcavator
HivExcavator

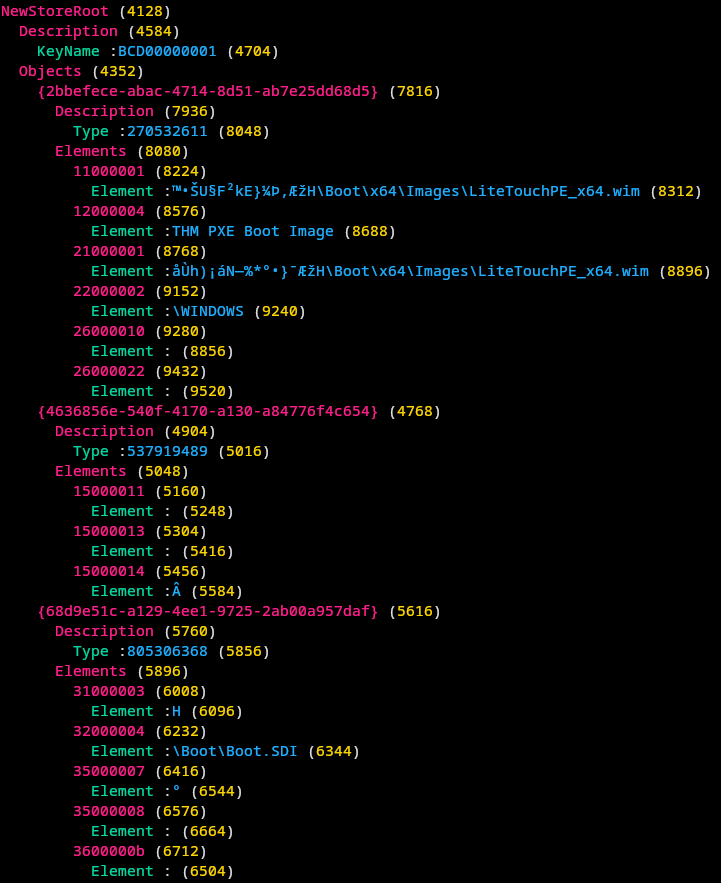
Extracting the contents of Microsoft Windows Registry (hive) and display it as a colorful tree but mainly focused on parsing BCD files to extract WIM files path for PXE attacks.
What is it?
Microsoft Deployment Toolkit (MDT) (integrated in System Center Configuration Manager (SCCM)) helps to automate the deployment of Windows and to manage OS images.
Some devices load and install the OS directly over a network connection via Preboot Execution Environment (PXE) images managed and hosted by MDT. Devices will ask a PXE configuration over Dynamic Host Configuration Protocol (DHCP) then a Trivial File Transfer Protocol (TFTP) connection is used to retrieve the PXE boot image.
Attackers are mainly interested in PXE boot images for:
- Modifying the image: injecting an Elevation of Privilege (EoP) vector or backdoor the image to gain administrative access or spy on the compromised host with a Man-in-the-Middle (MitM) attack.
- Read the image: parsing the image for passwords and secrets.
For the second scenario, the retrieved PXE configuration will give us a list of Boot Configuration Data (BCD) files used by Microsoft’s Windows Boot Manager.
Those BCD files are like databases and are using the same format as Windows Registry hives. Parsing the BCD files allows retrieving the path of Windows Imaging Format (WIM) files that are the bootable images (PXE boot images). Indeed, the BCD files retrieved via PXE will only contain the pointers towards WIM files and other stuff like System Deployment Image (SID) files.
Note: TFTP doesn’t allow to list available files so one has to know the exact path to retrieve them, that’s why parsing the BCD file is required.
After downloading the WIM files, the attack can parse them to retrieve, for example, credentials.
The PowerShell library PowerPXE does all that BUT while most functions (like Get-FindCredentials) work on PowerShell Core (open-source variant of PowerShell that runs on Linux and macOS), some functions like Get-WimFile only work on Windows PowerShell (the closed source variant of PowerShell that runs only on Windows).
Note: Get-WimFile, used to extract WIM file path, uses Common Information Model (CIM) PowerShell module that is available exclusively on Windows.
So while PowerPXE can be used to find and extract credentials from PXE server or detect BCD files on PXE server on Linux and macOS with PowerShell Core, it can’t export WIM path from BCD files on those OSes at it can only on Windows.
A Linux and macOS based attacker, certainly don’t want to create a Windows Virtual Machine (VM) only to parse a file, that is why HivExcavator is there: to allow you parsing BCD files on Linux and macOS to extract WIM files path.
Prerequisites
Install Hivex (part of libguestfs) because, unfortunately, the library and Ruby wrapper have not been made available as a gem.
Find the name of the package for your distro on Repology.
Installation
Quick installation:
- Satisfy the prerequisites
- Install the gem
$ gem install hivexcavator
Example
Example: hivexcavator ~/test/pxe/conf.bcd